Two weeks ago I attended a US Military tradeshow that showcased the latest and greatest cybersecurity technologies. As I sat and listened to the presenters the same question kept popping into my head. It is a question that has bothered me for some time and no vendor has been able to answer appropriately. I hit my breaking point when I heard a presenter discuss his company’s ability to put every packet in its own tunnel as part of something they call the Romulan cloaking technique (example of a bad analogy). So, after the presenter finished I raised my hand and asked my question, looking for King Arthur to extract the proverbial Excalibur from my brain (example of a good analogy).
“WHAT ABOUT LATENCY?”
Three simple but powerful words that show where cybersecurity has started to go wrong. How can you put every packet in its own tunnel without massively affecting network performance? Does user experience even matter anymore?
Click to Subscribe
Is it just me or are new cybersecurity products just rehashes of old cybersecurity products? We have gone from 128 bit encryption to 256 bit encryption. We have gone from endpoint protection to advanced endpoint encryption. We have gone from firewalls to next generation firewalls. We have gone from deep packet inspection to deeper packet inspection to deepest packet inspection. It is the same thing Hollywood did when they remade the greatest films of our generation like Ghostbusters and Vacation.
Do vendors stop and think about the effect they are having on network performance? Indeed a Cisco survey found that 71% of Chief Executives think that cybersecurity slows down the pace of commerce. So how are vendors improving cybersecurity without affecting latency? The answer seems to be more blade servers, faster processors, and ASICs. This may work but it also translates into higher costs for the customer. Are cybersecurity vendors starting to price themselves out of the market?
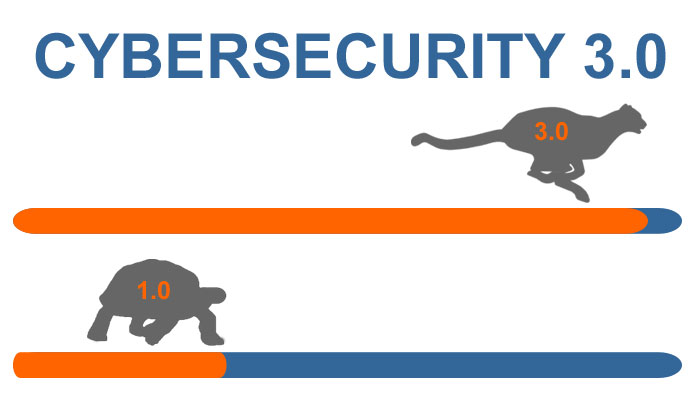
We need to rethink cybersecurity. We need to start designing solutions based on both network protection AND network performance. We need to look at our network from a holistic standpoint and identify existing tools that we can use for cybersecurity. Let’s call it Cybersecurity 3.0! (I know we skipped 2.0 but I was at a social media talk last week and the speaker used the term Web 3.0 so cybersecurity needs to catch up.)
In the next few weeks TELEGRID will be launching the first Cybersecurity 3.0 product which promises to turn the field of authentication on its head. If you are not on it already then Join Our Mailing List so you do not miss the release. In the meantime if you are looking for a secure authentication tool give me a call at 973-994-4440 and I will give you a sneak peek.
Eric Sharret is Vice President of Business Development at TELEGRID.
Click to Subscribe
Disclaimer: The opinions expressed here do not represent those of TELEGRID Technologies, Inc. The Company will not be held liable for any errors, omissions, or delays in this information or any losses, injuries, or damages arising from its display or use. All information is provided on an as-is basis.